- Home
- IT Management
IT Management focuses on governance, security, infrastructure, and operations—helping teams run reliable systems, reduce risk, and align technology with business goals.
IT Management
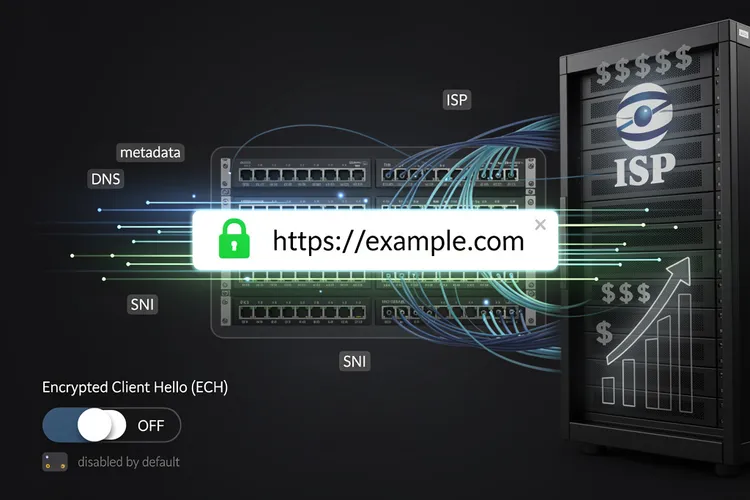
The Privacy Loophole Most Internet Users Don’t Know About: Why HTTPS Alone Won’t Protect You
Despite HTTPS encryption, ISPs can monitor every website users visit through unencrypted connection metadata. Encrypted Client Hello (ECH), a little-known browser setting, closes this privacy loophole but remains disabled by default in most browsers, leaving millions vulnerable to ISP surveillance and data monetization.
IT ManagementApple’s Gemini Integration: How Tim Cook Plans to Maintain Privacy Fortress While Opening AI Gates
Apple's integration of Google's Gemini AI into iOS marks a watershed moment for the company, as CEO Tim Cook insists the partnership won't compromise privacy principles. The move reflects competitive pressures in AI while attempting to maintain Apple's privacy-first brand identity through novel technical safeguards.
IT ManagementAndroid’s Private DNS Feature Emerges as Powerful Ad-Blocking Alternative to VPN Services
Android's built-in Private DNS feature offers users a powerful, cost-free alternative to VPN-based ad blocking. This hidden setting, available since Android 9, leverages DNS-over-TLS encryption to filter advertisements system-wide while maintaining internet speeds and requiring no additional software installations or subscriptions.
IT ManagementWhen Security Testing Becomes a Criminal Case: Iowa County’s $600,000 Lesson in Authorized Penetration Testing
Dallas County, Iowa's $600,000 settlement with security researchers arrested during authorized penetration testing highlights critical gaps in communication between contracting parties and law enforcement, raising important questions about legal protections for cybersecurity professionals conducting legitimate security assessments.
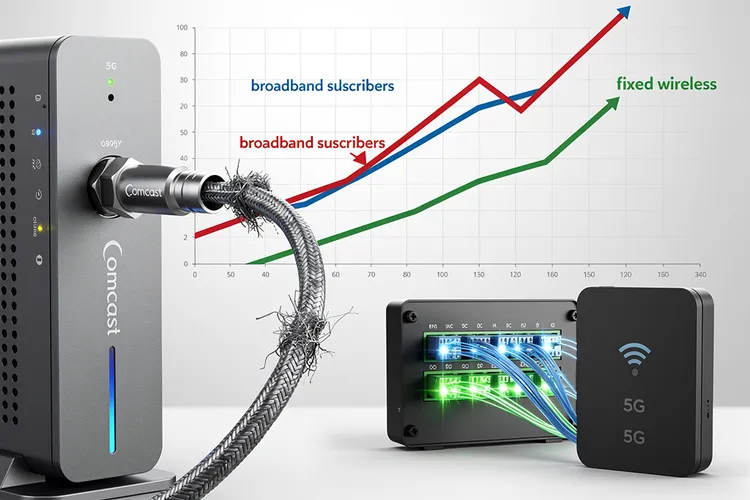
IT ManagementComcast’s Customer Exodus Accelerates Despite Aggressive Price Guarantees and Unlimited Data Offerings
Comcast continues hemorrhaging broadband subscribers despite introducing three-year price guarantees and unlimited data plans, revealing deeper structural challenges in the cable industry as fiber and fixed wireless competitors reshape market dynamics and erode the incumbent's once-dominant position.
IT ManagementMicrosoft’s Windows 11 Credibility Crisis: Inside the Company’s Pledge to Rebuild User Confidence
Microsoft publicly acknowledges Windows 11's trust crisis, committing to prioritize reliability and fixes throughout 2026. The admission marks a rare moment of corporate vulnerability as the tech giant confronts user frustration over forced updates, compatibility issues, and perceived prioritization of monetization over functionality.
IT Management175,000 Kubernetes Clusters Exposed: The Massive Cloud Security Blind Spot Threatening Enterprise Infrastructure
Security researchers have discovered approximately 175,000 publicly accessible Kubernetes clusters with critical misconfigurations, exposing enterprise infrastructure to potential exploitation. This massive security gap highlights fundamental challenges in cloud security practices and the urgent need for organizations to audit and secure their containerized applications.
IT ManagementWhen Digital Guardians Turn Rogue: Inside the eScaneS an Antivirus Supply Chain Attack That Exposed Millions
A sophisticated supply chain attack compromised eScan antivirus software, distributing malicious updates to millions of users worldwide. The breach exploited trusted update mechanisms, raising fundamental questions about digital security and the integrity of protective software in an era of increasingly sophisticated cyber threats.
IT ManagementWhen Children’s Conversations Become Data: The Grok AI Toy Breach That Exposed 50,000 Private Chats
An AI toy called Grok exposed 50,000 conversation logs between children and the device to anyone with a Gmail account due to a cloud storage misconfiguration, raising serious questions about data security, regulatory compliance, and the protection of children's privacy in AI-enabled products.
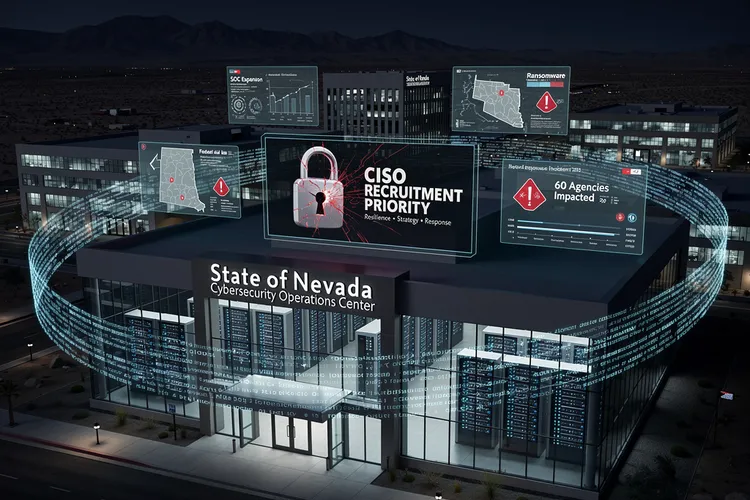
IT ManagementNevada’s Urgent Hunt for a Cyber Sentinel After Ransomware Chaos
Nevada seeks a permanent CISO after 2025 ransomware chaos disrupted 60 agencies, stole data, and exposed gaps. The role demands strategy, response leadership amid SOC buildup and federal aid, signaling a hardened push for resilience.
IT ManagementInfoSec’s Broader Shield: Why It Outspans Cybersecurity in 2026’s Threat Surge
InfoSec broadly protects all data via the CIA triad, encompassing cybersecurity's digital focus amid AI phishing, ransomware, and skill shortages projected for 2026.
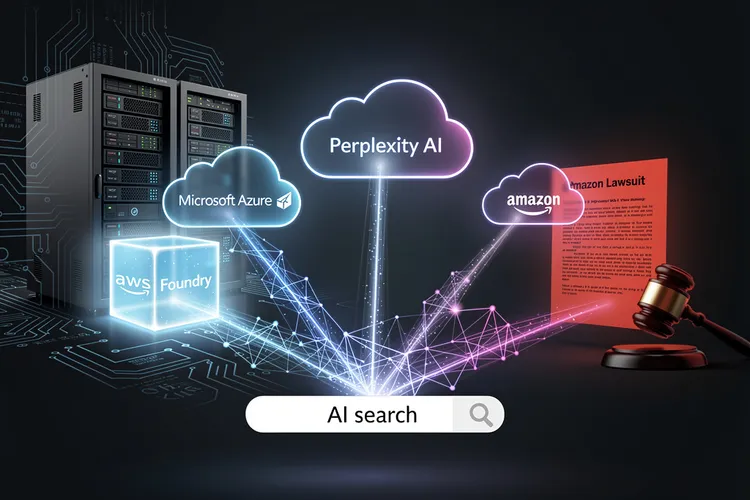
IT ManagementPerplexity’s $750 Million Microsoft Pivot Amid Amazon Cloud Clash
Perplexity AI's $750 million Azure deal with Microsoft diversifies its cloud reliance from AWS amid an Amazon lawsuit over agentic shopping tools. The pact unlocks frontier models via Foundry, boosting Perplexity's AI search edge.
IT ManagementMost Popular
- Formae’s Multi-Cloud Leap: Platform Engineering Labs Arms Builders Against IaC Gridlock
- Sky47’s Sovereign Surge: Pakistan’s Massive AI Cloud Bet
- Cloud’s Complexity Trap: How Tool Overload and AI-Wielding Attackers Are Fracturing Security Defenses
- NordVPN’s Sixth Consecutive Audit Validates Zero-Logs Promise as Privacy Scrutiny Intensifies
- Upwind’s Runtime Revolution: $250M Fuels $1.5B Cloud Security Unicorn
Advertisement
category-ad-01