- Home
- IT Management
IT Management focuses on governance, security, infrastructure, and operations—helping teams run reliable systems, reduce risk, and align technology with business goals.
IT Management
The Code War: Inside the Pentagon’s Aggressive Shift to Offensive Cyber Operations
The Pentagon has shifted from reactive cyber defense to aggressive "Defend Forward" operations, treating code as a kinetic weapon. This deep dive explores the strategic pivot, the integration of AI, the friction with Silicon Valley, and the high-stakes shadow war currently waging across global critical infrastructure networks.
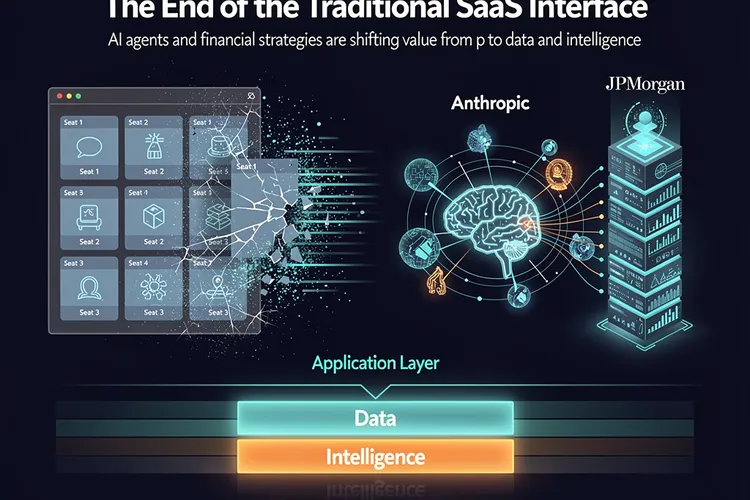
IT ManagementThe Great Interface Erosion: Why AI Agents Are Poised to Devour Enterprise SaaS
A deep dive into how AI agents from Anthropic and strategies from JPMorgan are signaling the end of the traditional SaaS interface. As AI moves from chatbots to autonomous workers, the seat-based software model faces an existential threat, shifting value from the application layer to data and intelligence.
IT ManagementWindows 11’s Gaming Gains Overshadowed by Stability Crisis: Performance Tests Reveal a Troubled Transition
Windows 11 version 24H2 delivers measurable gaming performance improvements over Windows 10, with frame rates up to 8% higher in testing. However, widespread Blue Screen of Death errors and stability issues are undermining user confidence and delaying adoption among gamers and enterprises alike.
IT ManagementCalifornia’s Delete Act Promises Privacy Revolution, Yet Implementation Reveals Deeper Cybersecurity Challenges
California's Delete Act enables residents to request deletion of personal data from hundreds of brokers with one click, but implementation reveals significant gaps in privacy protection and enforcement challenges that may require more comprehensive regulatory solutions.
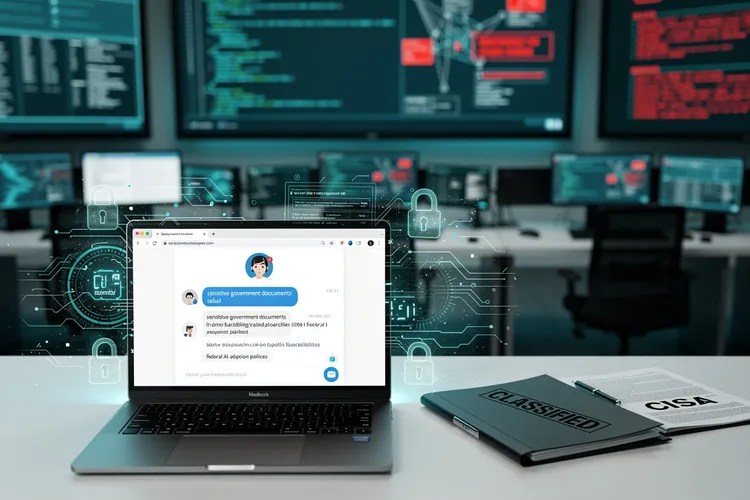
IT ManagementWhen the Watchdog Stumbles: Inside the ChatGPT Security Breach That Exposed Federal Cybersecurity Vulnerabilities
The acting director of CISA allegedly uploaded sensitive government documents to ChatGPT, exposing critical vulnerabilities in federal AI adoption policies. This incident reveals systemic gaps in cybersecurity protocols as agencies struggle to balance innovation with national security requirements.
IT ManagementMicrosoft’s Quiet Exodus: Why Enterprise Developers Are Abandoning Windows for Linux Workstations
Microsoft developers are increasingly abandoning Windows for Linux workstations, driven by performance gains, cloud-native development requirements, and reduced friction. This shift reflects fundamental changes in software development practices and Microsoft's own pragmatic embrace of platform independence.
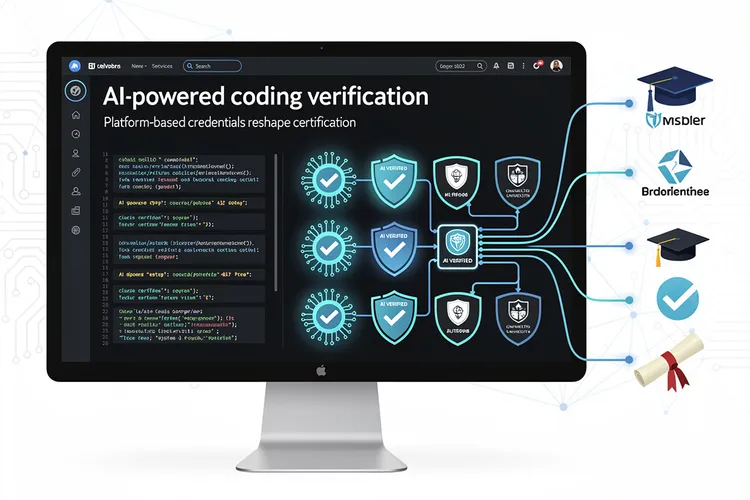
IT ManagementLinkedIn’s AI Verification Push Signals Shift in Professional Credentialing as Platform Battles Skills Inflation
LinkedIn introduces AI-powered coding verification badges to combat skills inflation and help employers identify genuine technical expertise. The move signals a broader shift toward platform-based credentialing that could reshape professional certification markets and challenge traditional education's role in validating competence.
IT ManagementGoogle Cloud’s Leadership Shake-Up: Hayete Gallot’s Departure Signals Strategic Pivot in Enterprise Customer Relations
Google Cloud's Customer Experience President Hayete Gallot has departed after less than two years, signaling a potential strategic shift in how the cloud division approaches enterprise customer relations amid intense competition from AWS and Microsoft Azure.
IT ManagementThe Hidden Threat in Your Search Results: How Mac Malware Infiltrates Google’s Advertising Ecosystem
Cybercriminals are exploiting Google's advertising platform to distribute sophisticated Mac malware through sponsored search results, undermining user trust and challenging Apple's security model. This investigation reveals how attackers leverage premium ad placements to reach valuable targets.
IT ManagementAutomation Platform n8n Patches Critical Flaws That Exposed Enterprise Workflows to Remote Takeover
Two high-severity vulnerabilities in the n8n workflow automation platform could have allowed attackers to execute arbitrary code and steal credentials, highlighting growing security challenges in enterprise automation tools. The flaws underscore the critical need for enhanced security practices in low-code platforms.
IT ManagementInside Mustang Panda’s Arsenal: How China’s Elite Hackers Refined Their Most Persistent Malware
Chinese state-sponsored hacking group Mustang Panda has deployed enhanced versions of its TONESHELL backdoor and PlugX malware, incorporating sophisticated evasion techniques and modular architecture. The updates demonstrate continuous evolution in tradecraft targeting government and diplomatic entities worldwide.
IT ManagementPanera Bread’s 1.4 Million Record Data Breach Exposes Critical Vulnerabilities in Restaurant Chain Cybersecurity
Panera Bread faces a massive data breach exposing 1.4 million customer records, including names, emails, and addresses. The incident highlights critical cybersecurity vulnerabilities in the restaurant industry and raises urgent questions about consumer data protection.
IT ManagementMost Popular
- Formae’s Multi-Cloud Leap: Platform Engineering Labs Arms Builders Against IaC Gridlock
- Sky47’s Sovereign Surge: Pakistan’s Massive AI Cloud Bet
- Cloud’s Complexity Trap: How Tool Overload and AI-Wielding Attackers Are Fracturing Security Defenses
- NordVPN’s Sixth Consecutive Audit Validates Zero-Logs Promise as Privacy Scrutiny Intensifies
- Upwind’s Runtime Revolution: $250M Fuels $1.5B Cloud Security Unicorn
Advertisement
category-ad-01